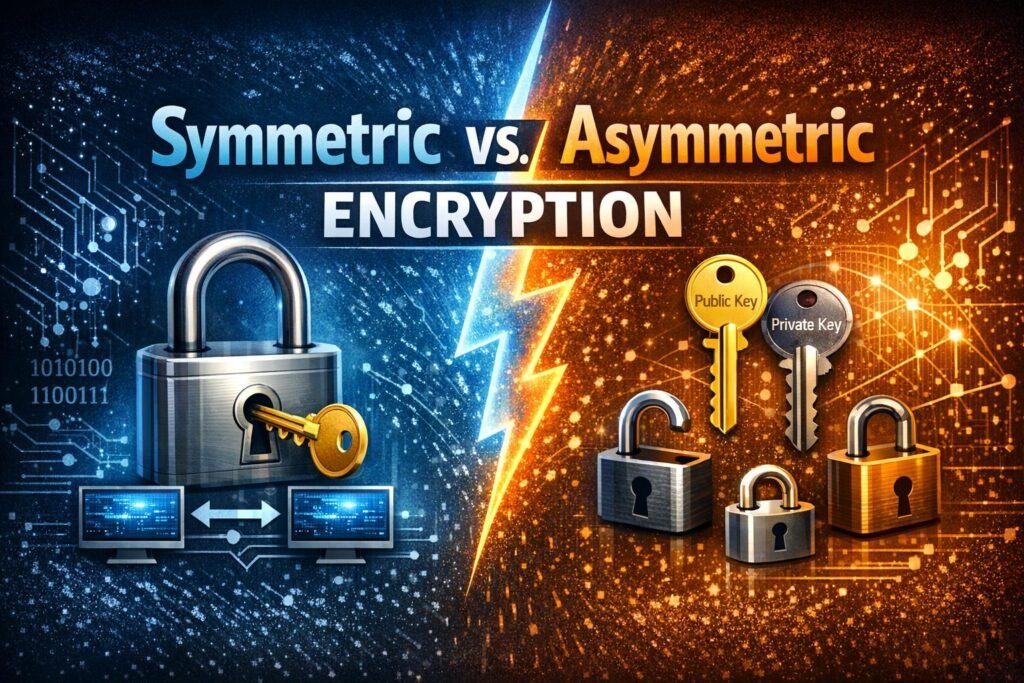
Symmetric vs. Asymmetric Encryption: Key Differences, Use Cases, and Why Both Matter
If you’ve ever wondered how your banking app stays secure or how HTTPS protects your login details, you’ve already encountered the practical impact of Symmetric vs. Asymmetric Encryption. These two cryptographic approaches quietly power almost everything we do online, yet they’re often misunderstood—or oversimplified. Imagine you are sending a physical chest full of gold across […]