If you’ve ever wondered how your banking app stays secure or how HTTPS protects your login details, you’ve already encountered the practical impact of Symmetric vs. Asymmetric Encryption. These two cryptographic approaches quietly power almost everything we do online, yet they’re often misunderstood—or oversimplified.
Imagine you are sending a physical chest full of gold across a dangerous territory. You have two choices. You can lock the chest and send the key via a separate messenger, hoping they aren’t intercepted. Or, you can use a magical chest that allows anyone to drop gold in and lock it, but only you possess the unique, master key to open it.
In the digital world, we deal with “gold” every second—our credit card numbers, private health records, and confidential business strategies. The methods we use to lock this data define the boundary between privacy and catastrophe. At the heart of this struggle lies the classic debate: Symmetric vs. Asymmetric Encryption.
Understanding these two pillars of cryptography isn’t just for developers or IT professionals; it’s for anyone who wants to understand how the modern internet actually functions. Let’s peel back the layers of the “crypto-onion” to see how these algorithms keep our secrets safe.
What is Symmetric Encryption? The Need for Speed
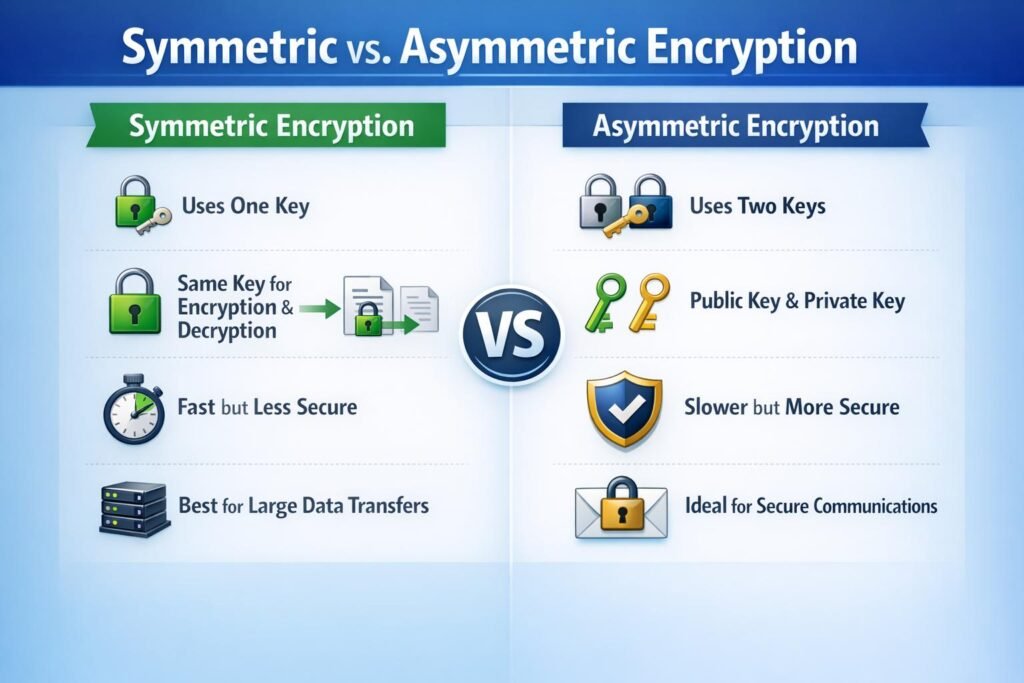
Symmetric encryption is the oldest and simplest form of cryptography. It relies on a single, shared secret key to both encrypt and decrypt information. Think of it like a traditional deadbolt on your front door: the same physical key that locks the door is the one used to unlock it.
In symmetric encryption, the same secret key is used to encrypt and decrypt data. Algorithms like AES dominate this space because they’re fast and computationally efficient, a point consistently emphasized in industry comparisons.
Symmetric encryption thrives in performance-sensitive environments:
- Data at rest (disk or database encryption)
- VPN tunnels and internal networks
- Real-time communication streams
How It Works in Practice
When you use a symmetric algorithm, such as the Advanced Encryption Standard (AES), the sender and the receiver must already possess the same key. The sender uses this key to scramble the plaintext into ciphertext. Once the receiver gets the message, they apply that exact same key to unscramble it.
Because the mathematical operations involved in symmetric encryption are relatively straightforward—often involving bitwise substitutions and permutations—they are incredibly fast. This makes symmetric encryption the “workhorse” of the data world.
The “Achilles’ Heel”: Key Distribution
The brilliance of symmetric encryption is also its greatest weakness. If I want to send you an encrypted file, how do I give you the key? If I send the key over the internet, a hacker could intercept it. If the key is compromised, the entire security chain collapses. This is known as the Key Distribution Problem, and it’s why symmetric encryption alone couldn’t power the global internet.
Enter Asymmetric Encryption: The Revolution of Public Keys
In the late 1970s, researchers Whitfield Diffie, Martin Hellman, and Ralph Merkle (along with RSA creators Rivest, Shamir, and Adleman) solved the distribution problem by introducing Asymmetric Encryption, also known as Public Key Cryptography.
Instead of one key, asymmetric encryption uses a mathematically linked pair of keys:
- The Public Key: This can be shared with anyone in the world. Its only job is to encrypt data.
- The Private Key: This must be kept secret by the owner. Its job is to decrypt data encrypted by its corresponding public key.
The Mailbox Analogy
Think of a public key like a mailbox slot. Anyone can walk up to your house and drop a letter through the slot, but once it’s inside, only you—the person with the private key to the back of the box—can retrieve and read the mail.
Asymmetric encryption, using protocols like RSA or Elliptic Curve Cryptography (ECC), allows two parties who have never met to establish a secure connection without ever sharing a secret key in advance. However, this security comes at a cost: the math is significantly more complex, making it much slower than symmetric methods.
Symmetric vs. Asymmetric Encryption: A Side-by-Side Comparison
To help you decide which method fits a specific use case, let’s look at the technical and operational differences.
| Feature | Symmetric Encryption | Asymmetric Encryption |
| Key Usage | Single key for both encryption & decryption. | Two linked keys (Public and Private). |
| Speed | Extremely fast; optimized for bulk data. | Slow; high computational overhead. |
| Key Management | Difficult; keys must be shared securely. | Easier; public keys are distributed freely. |
| Primary Use Case | Bulk data encryption (hard drives, databases). | Secure key exchange and digital signatures. |
| Algorithms | AES, DES, Blowfish, ChaCha20. | RSA, Diffie-Hellman, ECC, ElGamal. |
| Resource Usage | Low CPU and memory requirements. | High CPU and memory requirements. |
The Hybrid Reality: Why We Use Both
You might be wondering: “If symmetric is fast but hard to share, and asymmetric is slow but easy to share, which one does the internet use?”
The answer is both.
Most modern security protocols, like Transport Layer Security (TLS)—the “S” in HTTPS—use a hybrid approach. It uses hybrid encryption, combining both methods into a practical workflow. HTTPS is the clearest example. During a TLS handshake, asymmetric encryption securely exchanges a temporary session key, after which symmetric encryption takes over for high-speed data transfer.
When you visit a secure website, a “handshake” occurs:
- The Handshake: Your browser uses the website’s Asymmetric Public Key to securely send a small, temporary “session key” to the server.
- The Transition: Because only the server has the Private Key, it is the only one that can decrypt that session key.
- The Connection: Now that both your browser and the server have the same session key, they switch to Symmetric Encryption for the rest of the visit.
This gives us the best of both worlds: the unbreakable key distribution of asymmetric encryption and the blazing-fast performance of symmetric encryption.
This hybrid approach delivers:
- Trust without pre-shared secrets
- High performance at scale
- Reduced attack surface
Deep Dive: The Algorithms Shaping Our World
AES: The Gold Standard
The Advanced Encryption Standard (AES) is the symmetric algorithm used by governments and banks worldwide. It’s virtually uncrackable by today’s standards. Even with a supercomputer, it would take billions of years to brute-force an AES-256 key.
ECC: The Future of Asymmetric
While RSA has been the king of asymmetric encryption for decades, Elliptic Curve Cryptography (ECC) is rapidly taking over. ECC provides the same level of security as RSA but with much smaller key sizes. This means faster handshakes and less battery drain on mobile devices—a crucial factor in our “mobile-first” world.
A Personal Perspective: The Human Element of Encryption
Working in the tech industry, I’ve seen many organizations obsess over whether they should use AES-256 or RSA-4096, only to be compromised because an employee left their “Private Key” in a public GitHub repository.
The “Symmetric vs. Asymmetric” debate is a technical one, but the real-world application is often a human one. Encryption is only as strong as the key management behind it. Whether you are using a shared secret or a public-private pair, if the person holding the key isn’t careful, the math doesn’t matter.
We are moving toward an era of “Zero Trust,” where encryption isn’t just something we do at the perimeter of a network; it’s something that happens at every layer of data interaction.
Frequently Asked Questions
Is Asymmetric Encryption more secure than Symmetric?
Not necessarily. Security depends on key length and the algorithm used. A 256-bit symmetric key is roughly equivalent in strength to a 3072-bit RSA asymmetric key. Asymmetric isn’t “better”; it just serves a different purpose (key exchange vs. data locking).
What happens to encryption when Quantum Computing arrives?
This is a major concern. Quantum computers could potentially solve the math behind RSA and ECC very quickly. This is leading to the development of Post-Quantum Cryptography (PQC), which seeks to create asymmetric algorithms that even quantum computers can’t break.
Which should I use for my small business?
For storing files locally or on a cloud drive, use Symmetric Encryption (like BitLocker or FileVault). If you are communicating with clients or signing digital contracts, you will naturally be using Asymmetric Encryption via your email provider or digital signature service.
Final Thoughts: The Invisible Shield
The battle of Symmetric vs. Asymmetric Encryption isn’t a competition where one wins and the other loses. It is a partnership. Symmetric encryption provides the brute strength needed to protect massive amounts of data, while asymmetric encryption provides the sophisticated logic needed to communicate across a global, untrusted network.
The debate around Symmetric vs. Asymmetric Encryption misses the real story. One is not superior to the other—they solve different problems. Symmetric encryption brings speed and efficiency. Asymmetric encryption brings trust and scalability. Together, they form the backbone of modern digital security.
Understanding this partnership doesn’t just make you better informed—it makes you better prepared to design systems that last.
As we move deeper into the 2020s, with AI-driven cyberattacks and the looming shadow of quantum computing, understanding these foundations is your first line of defense.
Pingback: Roadmap to the Cybersecurity world - The Cyber Server