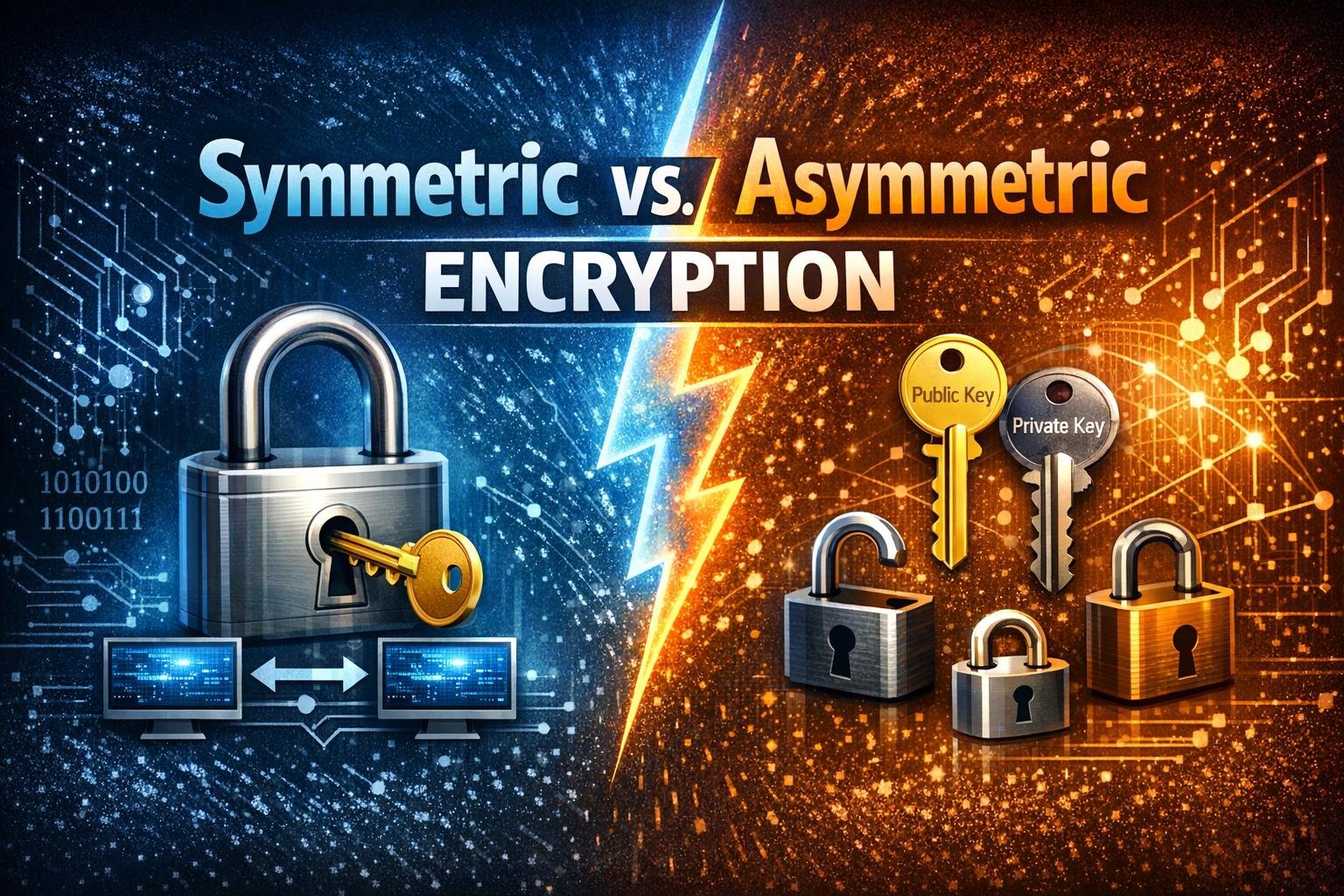
Symmetric vs. Asymmetric Encryption: Key Differences, Use Cases, and Why Both Matter
If you’ve ever wondered how your banking app stays secure or how HTTPS protects your login details, you’ve already encountered…
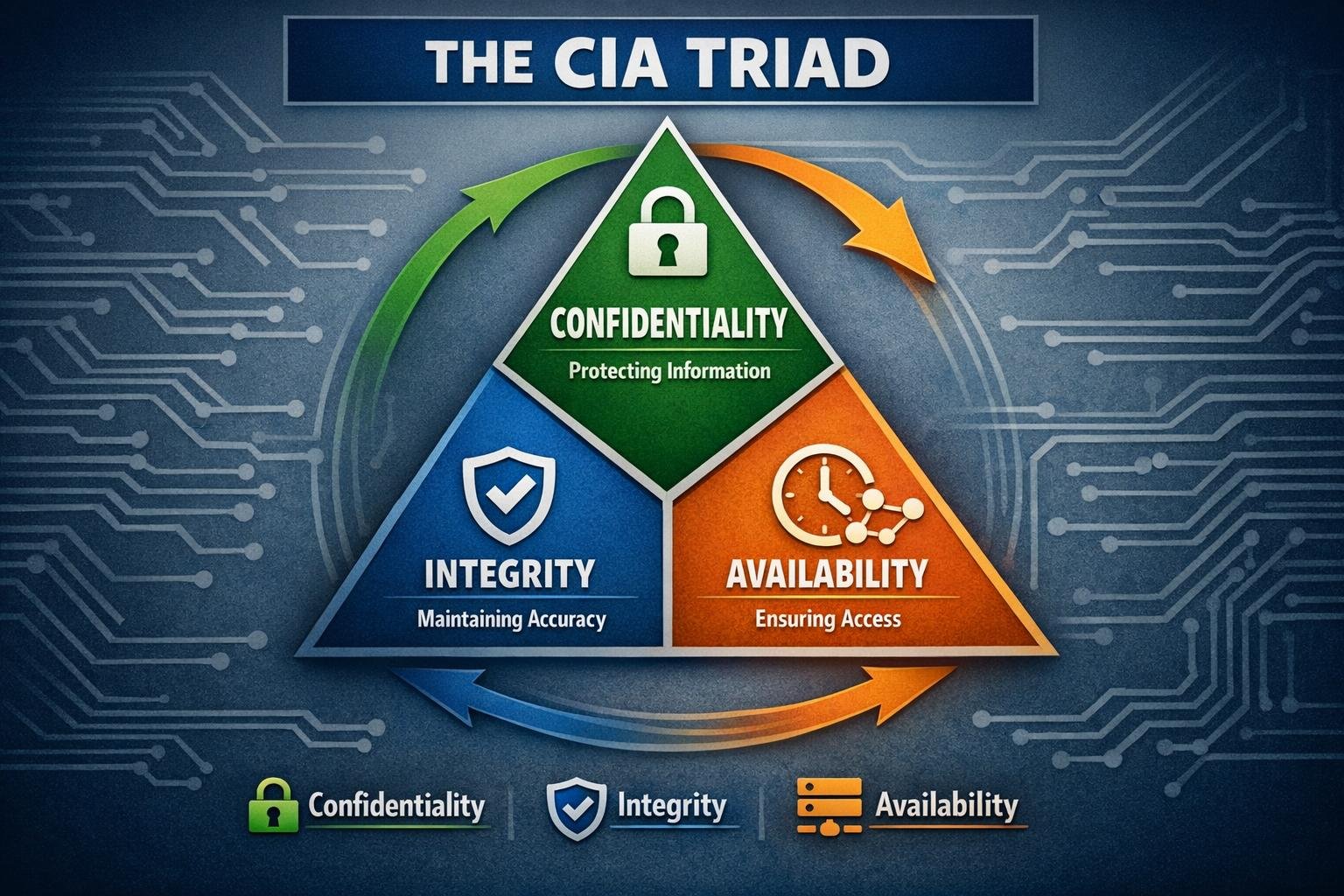
The CIA Triad: The Ultimate Guide to Confidentiality, Integrity, and Availability
Every time a major data breach makes headlines, the conversation quickly becomes cluttered—zero trust, AI-driven threats, ransomware-as-a-service, cloud misconfigurations. Yet,…
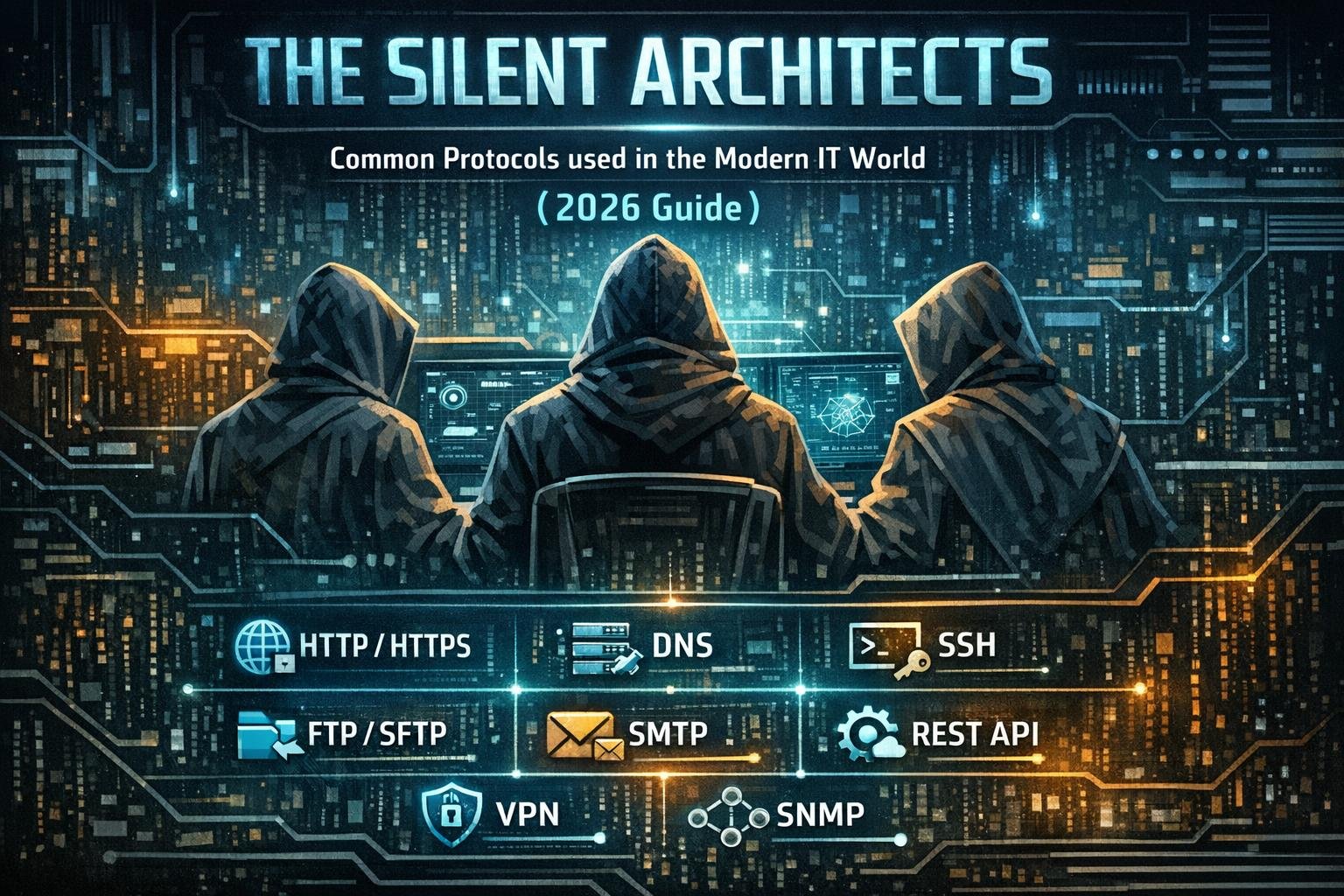
The Silent Architects: Common Protocols used in the Modern IT World (2026 Guide)
Every time you refresh a page, send a message, or stream a video, a silent, lightning-fast negotiation happens behind the…
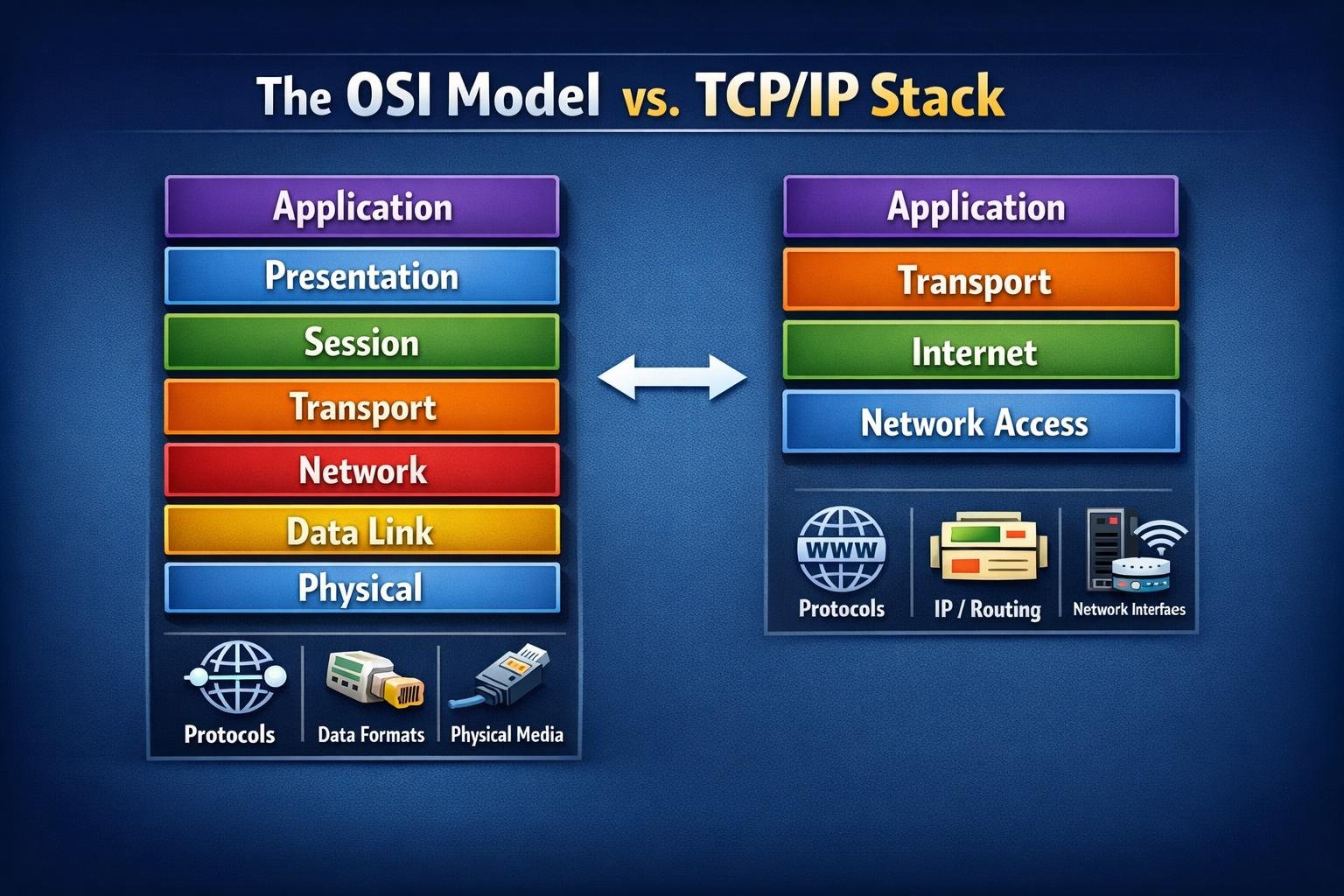
The OSI Model and TCP/IP Stack: The Ultimate Networking Blueprint
Have you ever paused to wonder how a simple tap on your smartphone screen in London can trigger a server…
Mastering Linux File System and Permissions: A Deep Dive Beyond ‘rwx’
Master the Linux File System and Permissions. A deep dive to the structural philosophy, user types, and deep permission mechanics…
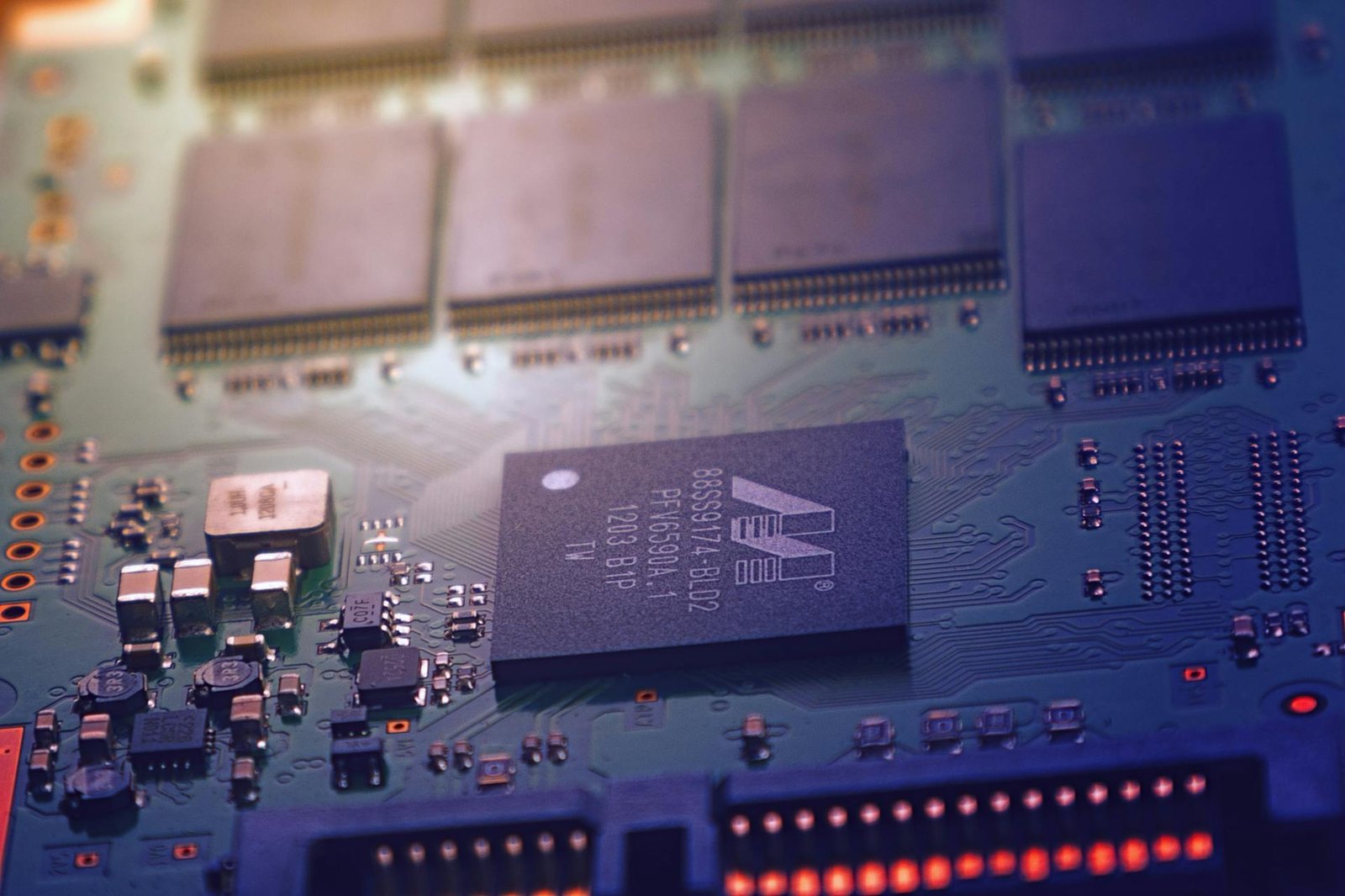
Computer Architecture and Hardware Basics
Imagine trying to be a world-class safe-cracker. You could read every manual on social engineering to trick guards, and you…