Imagine your network is a high-security gala. Without a guest list, anyone—from the local baker to a notorious jewel thief—could waltz through the front door. In the world of cybersecurity, that guest list isn’t just a piece of paper; it is a sophisticated, living set of instructions known as firewall rules.
While most people view a firewall as a simple “on/off” switch for the internet, professionals know the real magic lies in the granular details. Understanding Firewall Rules and Their Anatomy is the difference between a resilient infrastructure and a digital “open house” for hackers. It is not just about blocking the “bad guys”; it is about defining the very flow of your organization’s digital lifeblood.
Read more about Theory related to Firewalls here!
The Philosophical Core: Why Rules Matter
Before we dissect the components, we must understand the philosophy that governs them. Most modern security frameworks, including the Zero Trust architecture championed by NIST, rely on the “Principle of Least Privilege.” This means a firewall rule should only exist if it is absolutely necessary for a specific business function.
A firewall is essentially a policy enforcement point. Every packet of data that tries to cross from one zone (like the scary public internet) to another (like your private database) is interrogated. The firewall asks, “Who are you, where are you going, and what are you carrying?” The answers determine if the packet is allowed through or dropped into the digital abyss.
Read more about Networking Fundamentals here!
Dissecting the Body: Firewall Rules and Their Anatomy
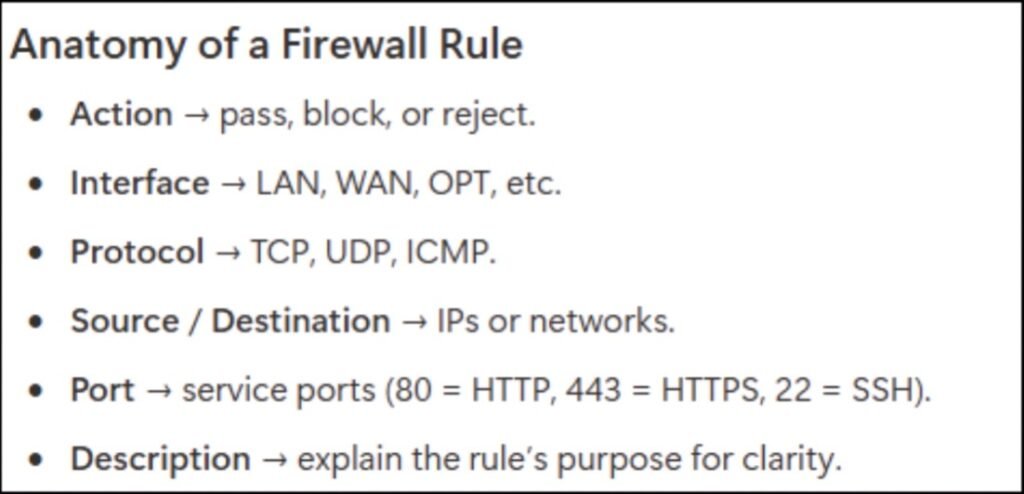
To manage a network effectively, you have to look under the hood. Every firewall rule, regardless of the vendor—be it Cisco, Palo Alto, or Fortinet—shares a common DNA. This “anatomy” is what allows the system to make split-second decisions on millions of packets per second.
1. The Source: Who is Asking?
The source defines the origin of the traffic. This isn’t always a single IP address. In complex environments, the source might be an entire subnet, a specific user identity authenticated via Active Directory, or even a geographic location.
Expert Insight: Relying solely on IP addresses is a legacy approach. Modern “Identity-Aware” rules look at the user’s role. For example, the “Accounting Department” group can access the payroll server, but the “Guest Wi-Fi” group cannot.
2. The Destination: Where is it Going?
Just as we define where traffic comes from, we must define its terminus. Is the packet headed for a public web server, an internal file share, or a cloud-based SaaS application? Specificity here prevents “lateral movement,” a technique where hackers jump from a compromised low-security device to a high-value target.
3. Protocol and Service (The Port)
This is the “how” of the communication. Protocols like TCP and UDP act as the transport mechanism, while ports act as the specific doors.
- Port 80/443: Web traffic (HTTP/HTTPS).
- Port 25: Email (SMTP).
- Port 22: Secure shell (SSH).
If you leave Port 22 open to the entire internet, you are essentially leaving your back door unlocked in a high-crime neighborhood.
4. The Action: The Ultimate Verdict
Once the firewall matches a packet to a rule, it must take action. There are generally three options:
- Allow/Permit: The packet passes through.
- Deny/Block: The packet is stopped, and usually, a “destination unreachable” message is sent back (which can actually give hackers information).
- Drop: The packet is silently discarded. This is often preferred for external-facing rules because it makes your network look like a “black hole” to scanners.
5. Logging and Inspection
A rule that doesn’t log is a missed opportunity for intelligence. Logging allows administrators to audit traffic patterns and troubleshoot connectivity issues. Advanced rules also include “Security Profiles,” which tell the firewall to scan the allowed traffic for viruses, vulnerabilities, or malicious file types.
Comparison: Stateless vs. Stateful Inspection
Not all firewalls read the anatomy of a rule in the same way. Understanding the evolution of these technologies helps in choosing the right defense strategy.
| Feature | Stateless Filtering | Stateful Inspection | Next-Generation (NGFW) |
| Context Awareness | None. Inspects packets in isolation. | High. Remembers the “state” of connections. | Deep. Understands applications and users. |
| Security Level | Low. Easy to spoof. | Medium. Protects against many scan types. | High. Can block specific features within apps. |
| Performance | Extremely fast. | Moderate. | Resource-intensive (requires specialized hardware). |
| Anatomy Focus | Basic 5-tuple (IPs, Ports, Protocol). | Connection tracking + 5-tuple. | Layer 7 (Application) + Identity + Content. |
Examples of Firewall Rules
Here are four common examples that represent the standard lifecycle of network traffic.
1. The “Web Access” Rule (Outbound)
This is the most common rule. It allows internal users to browse the internet safely.
- Source Zone: Internal_LAN
- Source IP: 10.0.5.0/24 (The Employee Subnet)
- Destination Zone: WAN (Internet)
- Destination IP: Any
- Service/Port: TCP 80 (HTTP), TCP 443 (HTTPS)
- Action: Allow
- Purpose: Let employees access websites while keeping other ports (like file sharing) closed to the outside world.
2. The “Database Protection” Rule (Internal/East-West)
In a secure “Three-Tier” architecture, your Web Server should be the only thing allowed to talk to your Database Server. This prevents a hacker who compromises the web server from easily wandering around the rest of the network.
- Source Zone: DMZ (Demilitarized Zone)
- Source IP: 192.168.1.10 (The Web Server)
- Destination Zone: Database_Zone
- Destination IP: 192.168.2.50 (The SQL Database)
- Service/Port: TCP 1433 (MS-SQL) or TCP 3306 (MySQL)
- Action: Allow
- Purpose: Strictly limits database access to a single “trusted” application server.
3. The “Block Malicious Actor” Rule (Inbound)
If your Security Information and Event Management (SIEM) system detects a brute-force attack coming from a specific IP address in another country, you would place this rule at the very top of your list.
- Source Zone: WAN (Internet)
- Source IP: 203.0.113.42 (The Attacker’s IP)
- Destination Zone: Any
- Destination IP: Any
- Service/Port: Any
- Action: Drop
- Purpose: To immediately “black hole” all traffic from a known threat before it can even try to authenticate.
4. The “Cleanup Rule” (The Safety Net)
This is always the final rule in a professional configuration. If a packet hasn’t matched any “Allow” rules above it, this rule catches it.
- Source Zone: Any
- Source IP: Any
- Destination Zone: Any
- Destination IP: Any
- Service/Port: Any
- Action: Deny & Log
- Purpose: Ensures that anything not explicitly permitted is blocked by default. Logging this rule is vital for spotting unauthorized connection attempts.
The “Order of Operations” Problem
A common mistake in managing Firewall Rules and Their Anatomy is ignoring the sequence. Firewalls read rules from the top down, like a checklist. The first rule that matches the traffic is the one that gets applied.
The Shadowing Trap
Imagine you have a rule at line #5 that allows all traffic to your web server. Then, at line #10, you add a rule to block a specific malicious IP address from reaching that same server. Because the “Allow” rule is higher on the list, the “Block” rule will never be triggered. This is known as “rule shadowing,” and it is a leading cause of accidental security gaps.
The Cleanup Rule (Implicit Deny)
Every well-configured firewall ends with what we call the “Cleanup Rule.” This is a “Deny All” rule at the very bottom. If a packet hasn’t matched any of your specific “Allow” rules by the time it reaches the end of the list, it is automatically rejected. This ensures that only explicitly authorized traffic enters your network.
Fresh Perspectives: Beyond the Basics
To truly master firewalling, we need to look at the “soft” side of rule management—the human and procedural elements that often fail before the technology does.
Rule Bloat and Digital Hoarding
In my experience working with enterprise networks, the biggest threat isn’t a zero-day exploit; it’s “Rule Bloat.” Over five or ten years, administrators add thousands of rules for temporary projects but never delete them.
This creates a “Swiss Cheese” effect where the firewall becomes so complex that no one actually knows what is being allowed. Periodically performing a firewall audit is essential. If a rule hasn’t seen a “hit” in 90 days, it’s a candidate for decommissioning.
The Rise of Layer 7 Awareness
Traditional firewalls were “blind” to what was happening inside a port. For example, if you allowed Port 80, a user could browse a website, but a hacker could also tunnel an unauthorized file transfer through that same port.
Modern Firewall Rules and Their Anatomy include “App-ID” or Application Control. This allows you to say: “Allow the marketing team to use Facebook, but block Facebook Games and Facebook Messenger.” This level of surgical precision is the new standard for internal security.
Read more about Networking Fundamentals here!
Best Practices for Crafting Resilient Rules
- Be Specific: Never use “Any” in the Source or Destination fields unless it is absolutely unavoidable (like a public-facing web server).
- Use Comments: Always document why a rule was created. Six months from now, “Rule for Project X” will mean nothing to your successor.
- Group Objects: Instead of writing 50 rules for 50 different servers, create a “Server Group” object and write one rule for the group. This makes the policy easier to read and manage.
- Test in “Alert Only” Mode: When deploying a new, complex rule, set the action to “Allow” but enable heavy logging first. This lets you see what would have been blocked before you actually break a critical business process.
Conclusion: The Living Firewall
Mastering Firewall Rules and Their Anatomy is not a “set it and forget it” task. It is a continuous cycle of refinement, observation, and adaptation. As threats evolve from simple port scans to sophisticated application-layer attacks, our rules must become more intelligent and identity-centric.
By treating your firewall rules as a precise architectural blueprint rather than a messy junk drawer of permissions, you create a foundation that can withstand the chaos of the modern threat landscape. Remember: a firewall is only as smart as the person who writes its rules.
Pingback: The Digital Sentry: Understanding Firewall, What It Is and How It Works in 2026 - The Cyber Server