Imagine you’re a developer working on the next breakthrough in fintech. You’re tired, it’s 2 AM, and you copy a block of proprietary code into a popular AI chatbot to help you debug a persistent error. In that instant, your company’s intellectual property (IP) has effectively left the building. Or, perhaps a marketing assistant accidentally CCs a public mailing list on an internal spreadsheet containing thousands of customer emails. These are the scenarios where DLP Policies matter the most.
These aren’t just “oops” moments; they are catastrophic security events. In 2026, where the boundary between “office” and “home” has vanished and data is the new oil, DLP Policies (Data Loss Prevention) act as the invisible digital guardrails keeping our most sensitive information from sliding off the cliff. Without them, even the most secure server is just a glasshouse waiting for a stone.
What are DLP Policies? The Rules of Engagement
At its simplest, a DLP policy is a set of conditions and actions. It asks the question: “Is this specific user allowed to move this specific data to this specific destination?” Modern DLP Policies are no longer just static “blocked words” lists. They are sophisticated, context-aware engines that use machine learning (ML) to distinguish between a routine file transfer and a potential data breach.
The Anatomy of a Policy
Every policy consists of three core elements:
- The Condition: What constitutes “sensitive” data? (e.g., Credit card numbers, HIPAA-protected health records, or
.envfiles). - The Context: Who is moving it, from where, and to whom?
- The Action: What happens when a match occurs? (e.g., Block the transfer, encrypt the file, notify IT, or ask the user for a business justification).
4 Essential Types of DLP Policies (With Examples)
If you are building your security stack on Cyber Server, you need to know that not all policies are created equal. Let’s break down the four pillars of modern data protection.
1. Regulatory & Compliance Policies
These are the “must-haves.” They are designed to keep your company out of legal trouble by ensuring you adhere to frameworks like GDPR, HIPAA, or PCI DSS.
- Example: A PCI DSS Policy scans every outbound email attachment. If it detects a string of 16 digits that passes the Luhn algorithm (indicating a credit card number), it automatically encrypts the email and sends a copy to the compliance officer.
- 2026 Insight: In 2026, these policies are increasingly automated. Leading platforms now offer “compliance packs” that automatically update whenever the EU or US government changes a privacy regulation.
2. Intellectual Property (IP) Policies
Your “secret sauce”—source code, CAD drawings, or strategic roadmaps—is what makes your business valuable. IP protection policies use Fingerprinting to recognize proprietary files even if they are renamed or slightly edited.
- Example: An IP Protection Policy creates a digital “fingerprint” of your primary source code repository. If a user tries to upload more than 10MB of similar data to a personal GitHub account or a USB drive, the system blocks the action and triggers an immediate high-priority alert for the Security Operations Center (SOC).
3. Behavioral & Insider Threat Policies
Sometimes, the threat isn’t the data itself, but the way it’s being accessed. User and Entity Behavior Analytics (UEBA) allows policies to detect anomalies.
- Example: A Departure Risk Policy monitors employees who have recently submitted their resignation. If an employee who usually accesses 10 files a day suddenly downloads 5,000 files in a single hour, the system locks their account and prevents any further data egress.
- Perspective: This isn’t about “spying”; it’s about risk mitigation. Most data theft occurs in the final 30 days of an employee’s tenure.
4. AI Governance & Shadow IT Policies
The newest challenge in 2026 is Shadow AI. Employees often use unauthorized AI tools to be more productive, unknowingly feeding corporate data into public models.
- Example: An AI Safety Policy detects when a user navigates to an unsanctioned LLM (Large Language Model) site. As the user types into the prompt box, the DLP agent “masks” or redacts any PII (Personally Identifiable Information) or API keys in real-time before the “Submit” button is clicked.
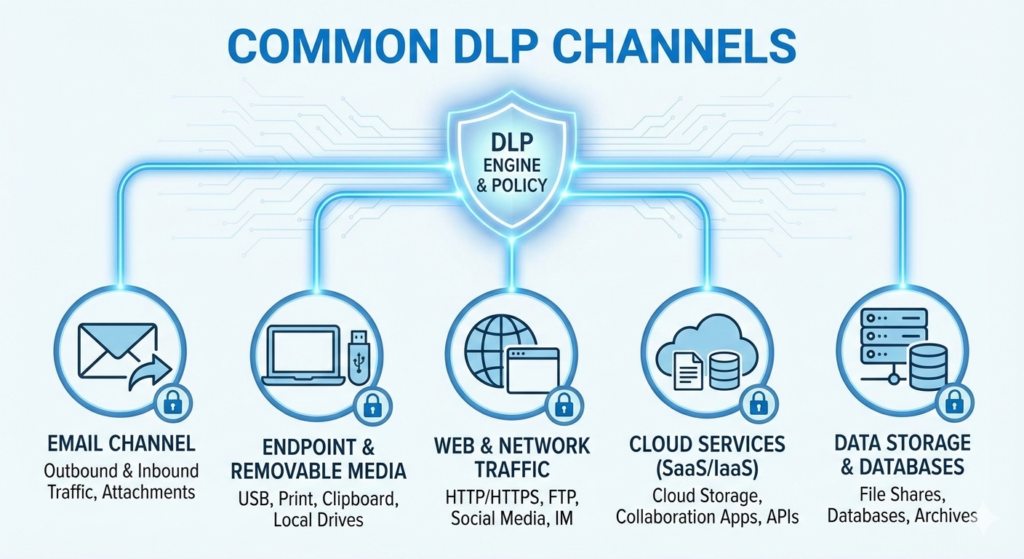
DLP Channels and DLP Policies
In a robust cybersecurity strategy, DLP Channels and DLP Policies are like the nervous system and the brain of your data protection framework. You can have the most brilliant security “brain” (Policies), but if it isn’t connected to the “limbs” (Channels), your data remains at risk.
Here is how these two critical components work together to form a seamless shield for your Cyber Server environment.
The Pathways vs. The Rules
To understand their relationship, think of Channels as the physical or digital roads data travels on, and Policies as the traffic laws and checkpoints governing those roads.
- DLP Channels (The “Where”): These are the exit points and storage locations. Whether it’s an outbound email, a Slack message, a USB stick, or a prompt into a Generative AI tool, the channel is the medium through which data moves.
- DLP Policies (The “What” and “How”): These are the intelligent instructions. A policy defines what data is sensitive (e.g., “anything looking like a private key”) and what should happen if that data is detected (e.g., “Block and alert the admin”).
The Interrelationship: Orchestration in Action
A common mistake in server management is treating channels in isolation. In a modern 2026 workflow, policies and channels are deeply interrelated through a concept called Multi-Channel Orchestration.
1. Policy Consistency Across Channels
If you have a policy that blocks “Customer PII” on the Email Channel but forget to apply that same policy to the Cloud Storage Channel, you’ve left a back door wide open. A well-designed DLP framework ensures that once a policy is created, it is “pushed” to every relevant channel simultaneously.
2. Contextual Awareness
The channel often dictates the severity of the policy action. For example:
- Internal Channel (Teams/SharePoint): The policy might simply Audit the movement of a technical spec file because the risk is low.
- External Channel (Personal Gmail/Web Upload): That same policy, seeing the same file, might trigger an immediate Block because the context of the channel suggests a high risk of exfiltration.
3. The “New Channel” Challenge: Generative AI
In 2026, the AI Prompt Channel has become a primary target for DLP policies. Because this channel is essentially a “web upload” disguised as a conversation, traditional network policies often miss it. Interrelating your Endpoint DLP (which sees the keystrokes) with your Cloud DLP (which understands the destination) is the only way to stop proprietary code from being leaked to public AI models.
Comparison: Policy Actions and Their Impact
| Action Type | What it Does | Best For… |
| Audit/Log | Records the event but allows the action. | Low-risk monitoring and policy testing. |
| Notify | Sends an alert to the user or IT. | Educating well-meaning employees. |
| Encrypt | Automatically wraps the data in a secure layer. | External emails containing sensitive records. |
| Justify | Asks the user “Why do you need to do this?” | Balancing productivity with security. |
| Block | Stops the transfer immediately. | High-risk intellectual property or PII leaks. |
Key Insights: Why “Block Everything” Is a Failing Strategy
In my years managing servers and security protocols, I’ve seen one mistake repeated more than any other: Over-aggressive blocking. If your DLP Policies are too strict, your employees will treat your security team like an obstacle. They will find workarounds—using personal phones to take photos of screens or using “Shadow IT” tools that bypass your network entirely.
Pro Tip: Focus on “Adaptive Protection.” In 2026, the best systems assign each user a “Risk Score.” If a user has a low score, they get more freedom. If they start exhibiting risky behavior, the policies automatically tighten up. This keeps the business moving while keeping the data safe.
The “False Positive” Nightmare
A poorly tuned policy can flag a random string of numbers as a credit card, blocking a critical invoice from being sent to a client. This is why Data Security Posture Management (DSPM) is becoming the standard. DSPM helps you understand where your data is first, so you can write more accurate policies with fewer false alarms.
Conclusion: Building Your 2026 Defense
Data protection is no longer a “one-and-done” checkbox. It is a living strategy that evolves as fast as the threats do. By implementing a mix of compliance, IP, behavioral, and AI-centric DLP Policies, you create a resilient environment where data can be used to its full potential without becoming a liability.
Remember, the goal of security is to enable the business to go faster, safely.